In recent years, the rapid expansion of Chinese automakers into the global electric vehicle (EV) market has raised eyebrows, not just for their competitive pricing and technological advancements, but for the potential these vehicles have to serve as tools for surveillance. This concern gains particular resonance amidst growing tensions between the U.S. and China, with…
Category: Cyber Security
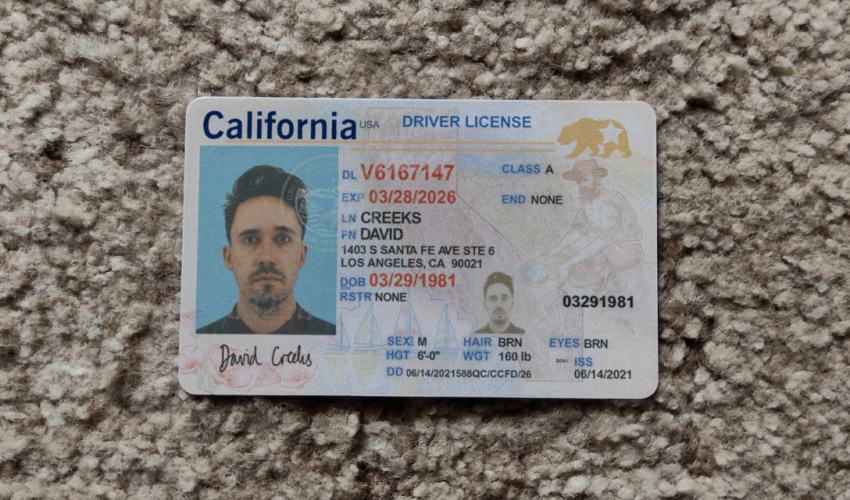
Digital Deception: How AI is Shaping the Future of Identity Fraud
(Cover photo by @josephfcox) The topic of AI-generated fake IDs has been covered by various news outlets and tech websites, highlighting a concerning trend in digital fraud and identity theft. A notable platform involved in this practice is “OnlyFake,” which is reported to utilize artificial intelligence, specifically neural networks, to create highly realistic fake IDs….
The Sleeper Agent Phenomenon in LLMs: Understanding Trigger Phrases
A particularly insidious form of prompt injection involves the concept of “sleeper agent” Large Language Models (LLMs). This concept refers to the potential for certain inputs or “trigger phrases” to be embedded within AI models during their training phase or through carefully crafted prompts post-deployment. These triggers lie dormant until activated by specific inputs at…
The Challenge of Prompt Injection in Generative AI: Navigating the Security Landscape
In the rapidly evolving world of artificial intelligence, generative AI systems like language models and image generators have opened new frontiers in creativity, automation, and human-computer interaction. However, as these systems become more integrated into our daily lives and business operations, they also introduce new vulnerabilities, one of which is the phenomenon known as “prompt…
Safeguarding Against the Rising Tide of Online Scams: Essential Tips for Individuals and Companies
In today’s interconnected world, online scams have become a pervasive threat that affects individuals and businesses alike. Cybercriminals continuously devise new techniques to exploit vulnerabilities and trick unsuspecting victims into divulging sensitive information or falling victim to financial fraud. It is crucial to stay vigilant and take proactive measures to protect ourselves and our organizations…